Ransomware Consolidation and Emerging Threats: Q1 2026 Analysis
Welcome to our deep dive into the ransomware landscape during the first quarter of 2026. This period saw a fascinating shift: after months of fragmentation, the ecosystem is now consolidating around a few dominant players. Attack volumes remain alarmingly high, with over 2,100 victims posted on data leak sites, making it the second-highest Q1 on record. New groups are emerging, established ones are evolving, and the overall threat shows no signs of slowing down. Below, we answer the most pressing questions about these trends.
How Did Ransomware Activity Change in Q1 2026?
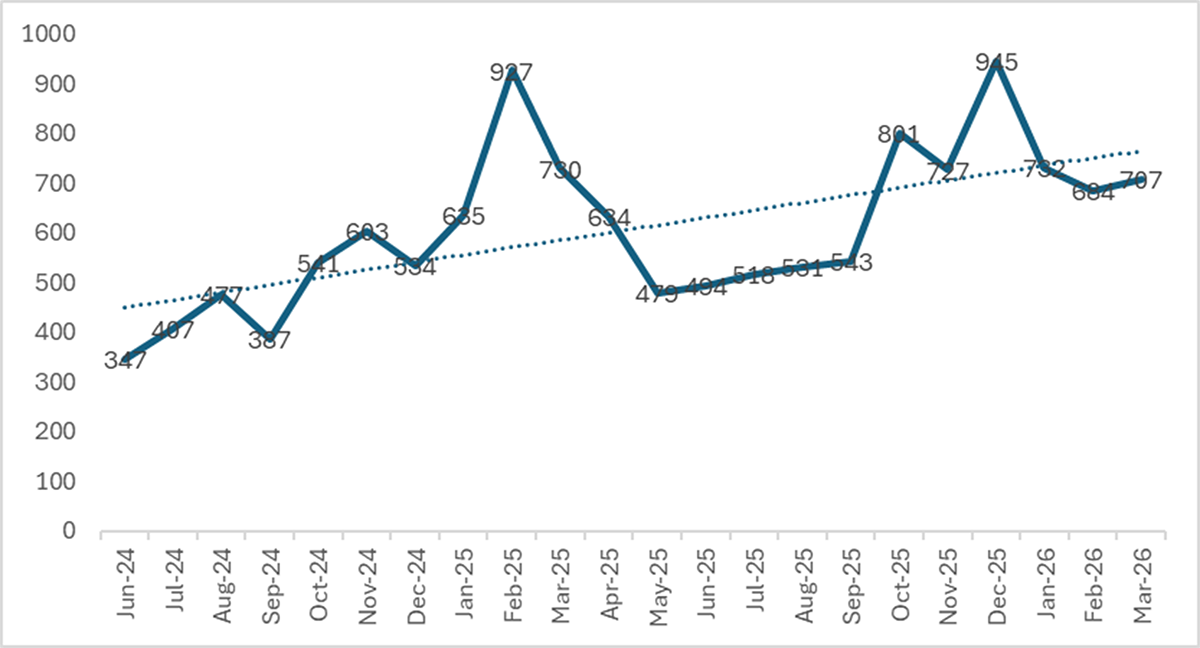
In Q1 2026, we tracked more than 70 active data leak sites (DLS) that collectively listed 2,122 new victims. This represents a 12.2% drop from the all-time record set in Q4 2025, but it's still the second-highest Q1 ever recorded and a staggering 117% above Q1 2024. Monthly volumes were remarkably stable: 732 victims in January, 684 in February, and 706 in March, averaging about 707 per month. The headline year-over-year comparison shows a 7.1% decline from Q1 2025, but that figure is misleading because Q1 2025 was inflated by Cl0p's massive Cleo exploitation campaign, which added roughly 390 victims in a single burst. When we exclude Cl0p from both periods, the actual year-over-year trend is an increase of 5.3%, indicating that underlying ransomware activity is still growing, even if extreme spikes have subsided.

What Does Consolidation Mean for the Ransomware Landscape?
The most significant structural shift in Q1 2026 is the move from fragmentation to consolidation. For over two years, the number of active ransomware groups had been steadily increasing—from 51 in Q1 2024 to a peak of 85 in Q3 2025. During that time, the top 10 groups' share of victims fell from 68% to 57%. But in Q1 2026, that trend reversed dramatically. The top 10 groups now account for 71.1% of all DLS-posted victims, the highest concentration since Q1 2024 when the ecosystem was much smaller. The total number of active groups shrank from 85 to 71, with 14 groups vanishing entirely while 21 new ones appeared. This consolidation suggests that larger, more sophisticated operations are absorbing territory from smaller players, leading to a more oligopolistic threat environment where resources and expertise are concentrated in fewer hands.
Why Is Qilin Still the Top Ransomware Group?
Qilin has maintained its position as the most dominant ransomware operation for the third consecutive quarter, posting 338 victims in Q1 2026. The group's sustained success can be attributed to its consistent operational tempo, effective leak site management, and ability to target a wide range of industries. Qilin likely benefits from a robust affiliate program that attracts skilled initial access brokers and penetration testers. While other groups have come and gone or suffered law enforcement takedowns, Qilin has remained agile, continuously adapting its tactics and infrastructure. The group's dominance is also a symptom of the broader consolidation trend: as smaller groups fade, Qilin absorbs their affiliate networks and victim pools, further concentrating power. For defenders, this means facing a more predictable but also more resilient adversary that can weather disruptions better than smaller, less established groups.
Who Was the Breakout Group in Q1 2026?
The standout newcomer in Q1 2026 is The Gentlemen, which rocketed to third place in the global ransomware rankings. The group dramatically increased its victim count from just 40 in Q4 2025 to 166 in Q1 2026—a more than fourfold surge. This explosive growth suggests that The Gentlemen either recruited a highly effective affiliate network, launched a series of targeted campaigns, or both. Unlike older groups that rely on legacy code or rebranded strains, The Gentlemen may be using novel evasion techniques or exploiting newly discovered vulnerabilities. Their rapid rise serves as a warning that the ransomware ecosystem remains highly dynamic, with new players capable of disrupting the established order. Security teams should monitor The Gentlemen's tactics, infrastructure, and targeted sectors closely, as they appear poised to become a persistent threat in 2026.
Is LockBit Making a Comeback?
Yes, LockBit's resurgence is confirmed in Q1 2026. After a period of diminished activity following law enforcement actions in 2024, LockBit posted 163 victims in the first quarter, climbing back to fourth place globally. This marks the emergence of LockBit 5.0, which appears to be a revamped version of the infamous ransomware strain. The group likely rebuilt its affiliate network and refined its encryption and evasion capabilities. LockBit's return is significant because it brings back a brand that was once the most prolific ransomware operation. Their comeback underscores the resilience of major cybercriminal enterprises: even after takedowns, decryption tools, and arrests, the brand can be revived if the underlying business model and codebase survive. This may prompt law enforcement agencies to intensify efforts to dismantle LockBit's infrastructure permanently.
How Does the Year-over-Year Comparison Change When Adjusted for Anomalies?
Raw year-over-year numbers can be deceptive. The headline shows a 7.1% decrease from Q1 2025's 2,285 victims to Q1 2026's 2,122 victims. However, Q1 2025 was heavily skewed by Cl0p's Cleo mass-exploitation campaign, which contributed approximately 390 victims in a single burst. When we remove Cl0p from both periods—since such external events don't represent organic ransomware growth—the comparison flips. In Q1 2025, excluding Cl0p left 1,894 victims; in Q1 2026, the total is 1,995. That's an actual year-over-year increase of 5.3%. This adjusted view reveals that the underlying ransomware trend remains upward, even as the most dramatic spikes have calmed. It also highlights the importance of context: policymakers and security vendors should base decisions on cleaned baselines rather than headline figures that may be distorted by single campaigns.